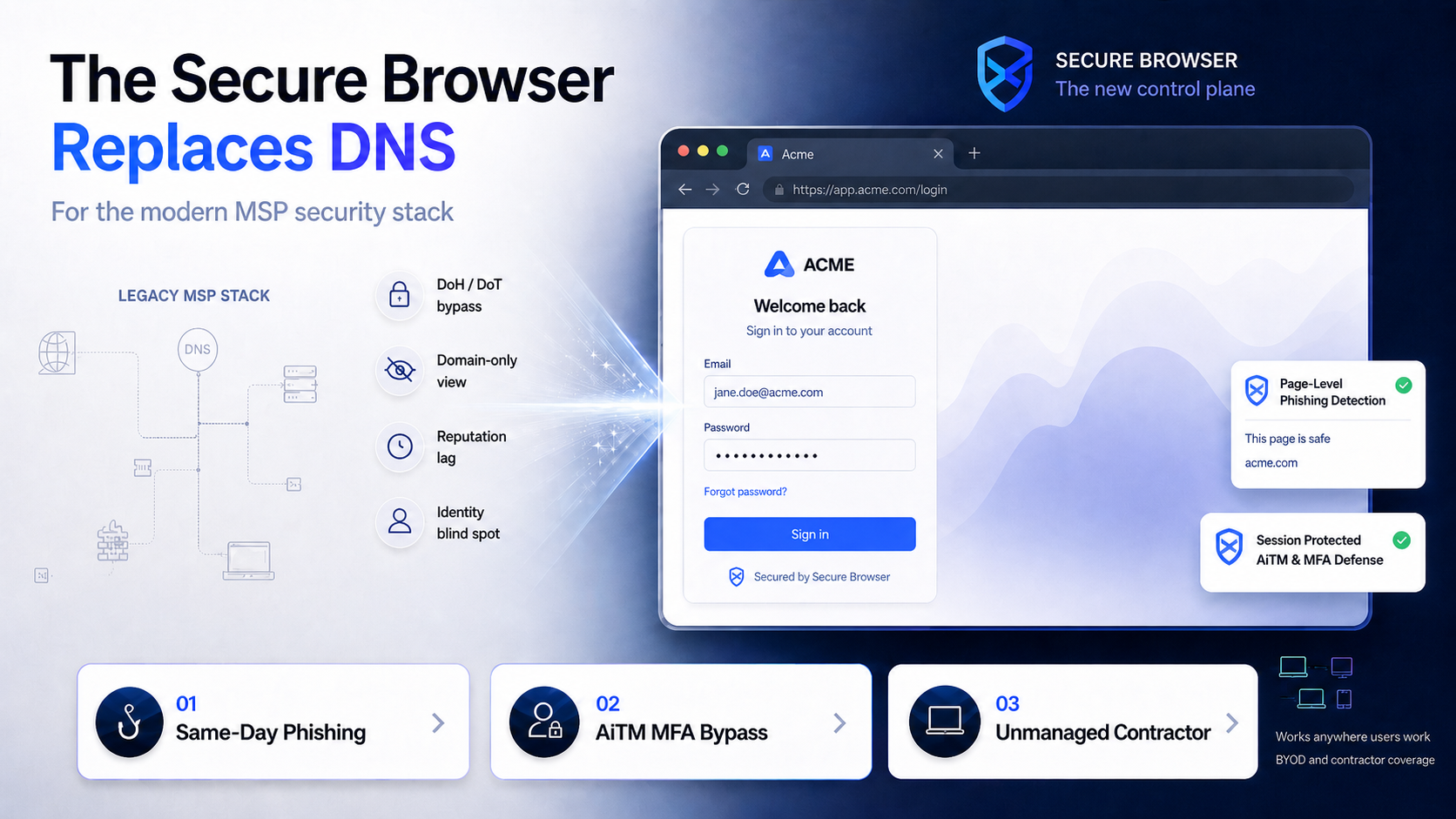
The modern MSP security stack includes a secure browser, not a legacy DNS appliance. The secure browser does everything DNS-layer filtering does, including domain blocking, category policy, allowlists, and denylists, and adds the protections DNS was never built to deliver: AI-based visual phishing detection at the page level, identity-aware controls at the SaaS login flow, and defense against the adversary-in-the-middle attacks that bypass MFA. The DNS box was built for a network that no longer exists. The browser is where the work, the threat, and now the control surface live.
WHY DNS IS NOW LEGACY The Network Box Was Built for a Network That No Longer Exists.
-
The encrypted-DNS bypass. Modern browsers ship with DoH and DoT enabled by default. Client traffic walks around the DNS forwarder before the appliance ever sees a query. The thing the MSP installed to enforce policy is the thing the browser is now ignoring.
-
The domain-only blind spot. DNS sees a hostname, not a page. It cannot read the form, see the rendered login, or notice that an OAuth consent screen is asking for read-mailbox scope. The malicious page on a clean domain looks identical to a legitimate one from where DNS sits.
-
The reputation lag. Modern phishing kits rotate domains in hours, sometimes minutes. By the time the threat feed catches up, the kit has already harvested credentials and moved to the next domain.
-
The identity-layer blackout. SaaS-era attacks happen at the SAML, OAuth, and MFA layers. DNS does not see SAML assertions, does not see OAuth scopes, does not see MFA prompts. The whole class of session-token theft is invisible from the network.
WHAT THE LEGACY STACK MISSES Four Attacks the DNS Box Watches Walk Through.
-
The same-day phishing kit. A new domain registered an hour ago, hosted on a reputable CDN, serving a pixel-perfect M365 login. DNS reputation has not tagged it. The user types their password. The browser is the only place the visual clone could have been caught.
-
The AiTM MFA bypass. The phishing kit is a transparent proxy. Username, password, and the MFA approval all flow through the attacker, who lifts the session token after the user clicks approve. DNS is not in the loop. EDR is not either.
-
The OAuth consent attack. A malicious app asks the user for full read-mailbox scope. The user clicks accept, no credentials are stolen, no DNS query looks suspicious. The attacker reads mail until someone audits app permissions weeks later.
-
The unmanaged contractor. A subcontractor logs into the client tenant from a personal laptop with no DNS forwarder, no EDR, and a residential network. The DNS box never sees the traffic. The browser would have.
Sources: DefensX MSP Buyer’s Guide 2025 | Microsoft Defender AiTM Phishing Trend Report 2024 | Google Transparency Report 2025 | Gartner Forecast: Enterprise Browsers as the Workforce Productivity Platform by 2030
THE FIX One Browser Layer Where the Threat, the Identity, and the Work All Live.
The DefensX secure browser collapses the legacy DNS stack into a single control plane on the device where users actually do their work. It enforces every category, allowlist, and denylist a DNS appliance does, and adds the controls DNS was never built to deliver: AI-driven visual inspection of the page itself, identity-layer awareness of OAuth and MFA flows, session-level policy that survives credential theft, agent-pinned enforcement on managed devices, and extension-only coverage on BYOD and contractor laptops.
Phishing on a Same-Day Domain.
Legacy DNS Stack
Reputation feeds have not tagged the new domain. The page is a pixel-perfect M365 login on a clean cert. DNS lets it through. The user enters credentials. The MSP finds out at the next breach review.
DefensX Secure Browser
AI visual inspection compares the rendered page against known-legitimate logins. The form is blocked at the input layer. The session never starts, the credentials are never typed, the MSP gets the event in the SOC console.
AiTM MFA Bypass.
Legacy DNS Stack
The phishing kit proxies the entire login. DNS sees a single hostname, EDR sees a routine browser process, and the attacker lifts the session token after the user approves the MFA prompt. The breach is discovered in the access logs, not the firewall.
DefensX Secure Browser
The browser detects the proxy pattern in the request flow, blocks credential submission before it leaves the page, and surfaces the attempt to the SOC console. The session token is never minted, the MFA prompt is never approved.
Unmanaged Contractor on a Personal Laptop.
Legacy DNS Stack
No DNS forwarder, no EDR, residential network. Every legacy network control is bypassed by definition. The MSP has no visibility, no policy, and no audit trail covering the contractor session inside the client tenant.
DefensX Secure Browser
The browser is the access point. Policy travels with the browser, no endpoint agent required. The contractor gets work done, the MSP gets policy enforcement, identity context, and a full audit trail.
WHAT THE BROWSER SEES THAT DNS DOESN’T Same Filtering Surface, Modern Threat Surface.
| Capability | Legacy DNS Stack | DefensX Secure Browser |
|---|---|---|
| Domain & category enforcement | Yes, at the resolver | Yes, enforced inside the browser |
| Encrypted DNS (DoH/DoT) bypass | Walked around by client browsers | Resolved and enforced locally |
| Visual page inspection | No, blind to page content | AI-driven render-time match against known logins |
| Identity-layer controls | No OAuth, SAML, or MFA visibility | Inline policy on consents and login flows |
| AiTM session-token theft | Invisible at the network layer | Proxy pattern detected, submission blocked |
| Unmanaged & BYOD coverage | Requires DNS forwarder or VPN | No endpoint agent required |
| Audit-ready evidence | Domain and IP logs only | Page, session, and identity events |
THE MSP OPERATIONAL PLAY Fewer Tools, Modern Coverage, Same Console.
- Fewer Tools, One Console – Drop the DNS appliance, the standalone phishing simulator, and the extension manager. The browser is one bill, one onboarding, one report per client.
- BYOD Feasibility – Light agent on managed fleets, extension-only on BYOD and contractor laptops. Personal devices are inside policy from day one, no DNS forwarder to ship.
- Audit Trail Clients Will Read – Page, identity, and session events captured at the browser. SOC 2 and NIS 2 evidence comes out of the same console as the policy.

