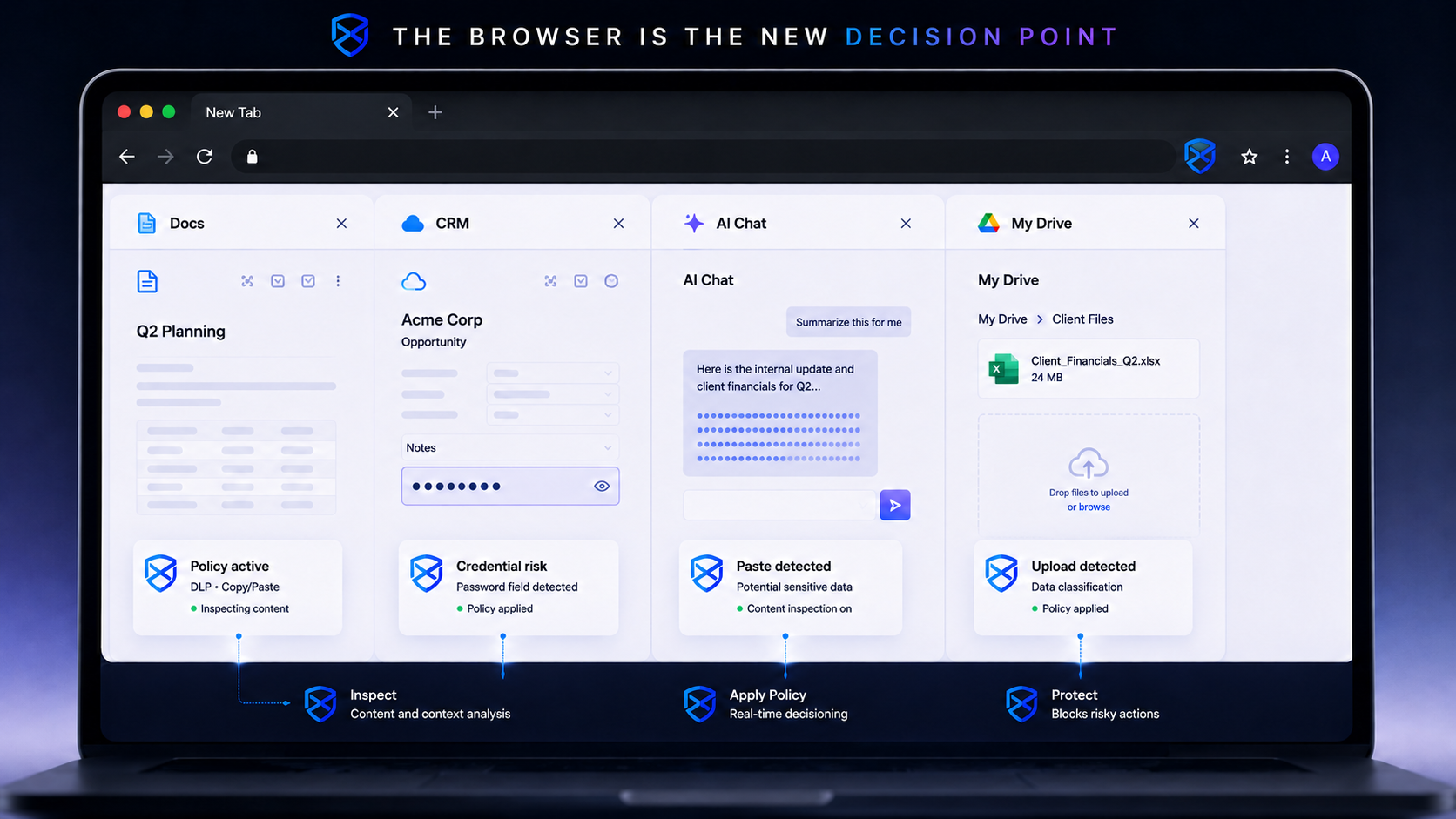
The way employees actually work has consolidated into a single application. The M365 tab, the Salesforce tab, the ChatGPT tab, the personal Drive tab, and the OAuth consent dialog all live side by side. Most risky actions an employee can take now happen between those tabs, often within the same minute. The page, the prompt, the upload, and the consent dialog are the places those actions are visible in real time.
WHERE RISKY ACTIONS ACTUALLY HAPPEN Three Categories, One Control Plane.
-
AI prompt leakage. Sales reps paste account lists into ChatGPT to draft outbound. Developers paste source code into Copilot to debug a build. Finance analysts paste budget tables into Claude to summarize a quarter. The data leaves at the speed of a keystroke, before any classifier in the network layer sees a request.
-
Data exfiltration through personal channels. A user uploads a client roster to a personal Drive folder to work from home. A subcontractor forwards an attachment to a private email. A marketing manager pastes a competitive deck into WeTransfer to share with an agency. None of these look unusual at the network layer.
-
Credential and consent hygiene. Users type a corporate password on a non-corporate login form. An OAuth consent prompt asks for full read-mailbox scope and gets clicked through. An MFA push appears at midnight and gets approved by reflex. Each one is a single browser action with months of consequence.
WHY LEGACY CONTROLS MISS THEM The Action Happens Above the Endpoint and Past the Network.
-
Network DLP terminates at TLS. Once traffic is encrypted, the network appliance sees a destination and a byte count. Modern SaaS, AI, and cloud-storage destinations look identical at that layer.
-
CASB operates at the API tier. CASB enforces policy at the OAuth and API edge of sanctioned apps. Pasting into ChatGPT, dragging into a personal Drive tab, or typing credentials into a clone domain happens outside that surface.
-
EDR watches processes. The endpoint agent sees chrome.exe running normally. The page that rendered, the form that submitted, and the file that uploaded are events taking place inside the process.
-
The action moves faster than the response. Most risky browser actions complete in under five seconds. Any control that has to ship telemetry, analyze it, and return a decision is reacting after the data has already left.
Sources: Verizon DBIR 2024 | IBM Cost of a Data Breach Report 2024 | Microsoft Defender AI Risk Survey 2025 | Gartner Forecast: Enterprise Browsers as the Workforce Productivity Platform by 2030
THE FIX One Control Plane Where the Action Actually Happens.
The DefensX secure browser inspects the work as it happens: the keystroke, the paste, the upload, the form submission, the consent click, the credential input. Policy runs at the moment of action, inside the same browser the employee already uses. Page-level inspection, AI prompt redaction, file flow control, OAuth scope review, and credential submission control all run in one console, on managed devices and BYOD alike.

Pasting Sensitive Data into an AI Tool.
Legacy Stack
A sales rep pastes a customer roster into ChatGPT to draft outreach. TLS to OpenAI looks normal at the network layer, no DLP signature fires. The data is inside the model provider within seconds. The MSP finds out at the next compliance audit, or never.
DefensX Secure Browser
The paste enters the browser before it enters the page. The classifier matches PII and account patterns. The paste is blocked or redacted at the field. The event is logged with user, time, and the redacted payload. The data never leaves the browser.
Uploading a Client File to a Personal Drive.
Legacy Stack
The user drags a client roster into a personal Google Drive tab. EDR sees chrome.exe running normally. The network sees TLS to drive.google.com, identical to the corporate Drive session. CASB has no policy on the personal tenant.
DefensX Secure Browser
The browser distinguishes the corporate tenant from the personal tenant by URL and account context. The upload is blocked or quarantined. A policy event surfaces to the MSP console with the file name, the destination tenant, and the source page.
OAuth Consent for a Malicious App.
Legacy Stack
A user clicks Accept on an OAuth consent dialog requesting full read-mailbox scope. No DNS query, no EDR signal, no network anomaly. The attacker reads mail for weeks until app permissions are audited.
DefensX Secure Browser
The browser inspects the consent dialog before it is approved. The requested scope is matched against the policy. High-risk consents are blocked or routed for step-up review. The grant never lands.
THE BEHAVIORS THE BROWSER SEES IN REAL TIME Same Place the Work Happens, Same Place the Policy Runs.
| Risky Action | Legacy Stack Response | DefensX Intervention |
|---|---|---|
| Paste of PII into AI prompt | Encrypted TLS, no payload visibility | PII classifier blocks or redacts at the field |
| Upload to a personal cloud tenant | Same TLS host as the corporate tenant | Tenant context separates corporate from personal |
| Credential on a non-corporate domain | DNS log clean, EDR sees a normal browser | Domain trust policy blocks credential submission |
| OAuth consent for a sensitive scope | No network or endpoint signal fires | Scope inspected, high-risk consents blocked |
| Source code pasted into AI assistant | Encrypted TLS, no content visibility | Source code patterns matched, paste blocked |
| File download from unverified domain | EDR sees the disk write after the fact | URL category enforced before the download starts |
| MFA push approved by reflex | No application or network signal | Browser surfaces context and step-up prompt |
THE MSP OPERATIONAL PLAY Fewer Tools, Modern Coverage, Real-Time Intervention.
- One Console for Behavior Policy – Browser-level rules govern paste, upload, consent, and credential events across every tab. AI risk, data exfiltration, and identity hygiene share one policy surface.
Detect the Action. Prevent the Exposure. Audit the Outcome.
One browser layer for AI risk, data exfiltration, and identity hygiene. MSP-native deployment, audit-ready by default.

